Stablecoins in B2B Payments: AML Risks, FATF Warnings, and Compliance Challenges
Phoebe Duong
Author

As stablecoins become more widely adopted in B2B payments and international trade, global financial regulators are also raising stronger warnings.
Recent reports from the Financial Action Task Force (FATF) and blockchain analytics firms such as Chainalysis highlight that stablecoins used in commercial payment flows could introduce new risks related to money laundering, fraud, and sanctions evasion, particularly when combined with cross-border transactions and unhosted wallets.c
This creates several important questions for businesses that are already using or planning to build stablecoin payment infrastructure:
- Why are stablecoins, a legitimate payment instrument, increasingly viewed as high-risk in B2B payments?
- What types of fraud and laundering schemes are emerging within stablecoin-based commercial transactions?
- How can companies unknowingly receive “dirty stablecoins” and face blacklist or asset freezes?
- And most importantly, what compliance and infrastructure measures should businesses implement to safely use stablecoins?
This article explores the latest warnings from FATF alongside on-chain intelligence to help businesses understand the real risks behind stablecoin-based B2B payments, and the compliance strategies needed to mitigate them.
Why FATF and Chainalysis Consider Stablecoins in B2B Payments High-Risk
The same characteristics that make stablecoins attractive for legitimate B2B payments also make them highly attractive to financial crime networks.
According to the Chainalysis 2026 Crypto Crime Report, illicit cryptocurrency activity reached approximately $154 billion in 2025, with stablecoins accounting for around 84% of illicit transaction volume.While stablecoins are also widely used for legitimate purposes, their structural properties create an environment where illegal funds can blend more easily with legitimate commercial transactions.
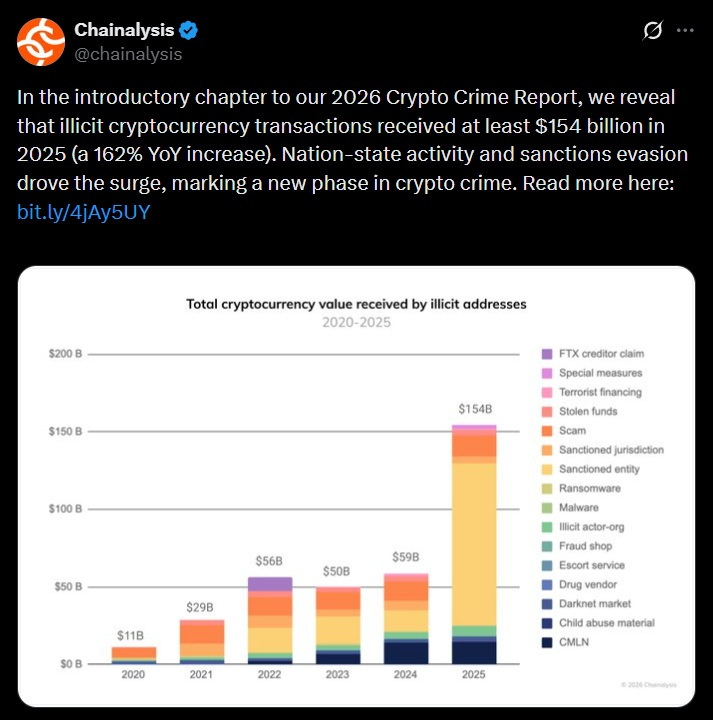
One of the key risks lies in how illicit actors can disguise transactions as legitimate B2B payments. Criminal groups can fabricate supplier relationships, generate fake invoices, or impersonate vendors to request payments in stablecoins such as USDT or USDC. On the surface, these transactions resemble ordinary commercial settlements. In reality, they serve as a mechanism to move and launder funds across borders.
Another challenge is the difficulty of tracing and recovering funds once large stablecoin transfers occur. In B2B environments, transactions often involve hundreds of thousands - or even millions of dollars. If a company unknowingly receives stablecoins linked to hacking incidents, scams, or sanctioned entities, the consequences can extend beyond a single transaction. Entire payment flows may become contaminated, potentially leading to wallet blacklisting or asset freezes by issuers.
This is why regulators increasingly emphasize that the primary concern is not stablecoins themselves, but their growing integration into mainstream financial and commercial infrastructure. As stablecoins move from niche crypto trading tools into large-scale payment rails for global commerce, the potential for money laundering, terrorist financing, and sanctions evasion can expand significantly if proper safeguards are not in place.
In other words, the risk does not emerge simply from criminal usage—it emerges from the intersection of legitimate commerce and illicit financial flows on the same infrastructure.
Why Companies Need Monitoring, Travel Rule, and Freeze Capabilities
Global regulators are tightening oversight of stablecoin payments as these assets become increasingly embedded in real-world commerce.
In its targeted updates on virtual assets, FATF also highlighted that the rapid global adoption of stablecoins could amplify financial crime risks if compliance frameworks remain inconsistent across jurisdictions.
For businesses processing cross-border stablecoin payments, this regulatory shift creates several external risks.
Travel Rule Enforcement
The Travel Rule requires regulated crypto service providers to share identifying information for both the originator and beneficiary of digital asset transfers between institutions.
In practice, this means payment infrastructure must support:
- Originator and beneficiary identity data
- Wallet attribution
- Inter-institution messaging for transaction metadata
Without these capabilities, companies facilitating cross-border stablecoin payments risk falling out of compliance with global AML standards.
The Risk of Frozen Funds
Stablecoin issuers also maintain the ability to freeze assets linked to sanctions violations or illicit activity.
Companies such as Circle and Tether have previously frozen wallets connected to hacks, scams, and sanctioned entities.
For businesses, this introduces a new operational risk:
receiving tainted funds can expose an entire treasury to sudden freezes or compliance investigations.
The Global Regulatory Wave
Regulatory pressure around stablecoins is also intensifying through new legislation across major jurisdictions.
In Europe, the Markets in Crypto-Assets Regulation (MiCA) introduces licensing, reserve transparency, and compliance obligations for crypto-asset service providers, effectively placing stablecoin-related payment infrastructure under financial regulatory oversight.
In the United States, proposed legislation such as the GENIUS Act aims to regulate fiat-backed stablecoins as a form of payment infrastructure, with requirements for issuer supervision, reserve backing, and anti-money-laundering controls aligned with the Bank Secrecy Act framework.
Regulatory alignment is also emerging across Asia. In Vietnam, the State Bank of Vietnam is expected to gradually align digital asset oversight with the standards set by the Financial Action Task Force under evolving regulatory frameworks such as Decree 52/2024 and upcoming guidance for digital payment and virtual asset activities. As cross-border stablecoin payments grow, businesses interacting with global partners may increasingly face AML screening and transaction monitoring expectations similar to those applied in regulated financial systems.
For detailed updates on Vietnam’s regulatory framework, refer to Decree 52/2024/ND-CP and the latest guidance related to digital assets. Fystack also provides a practical overview of custody compliance in Vietnam in “Vietnam Digital Asset Law 2026: A Guide to Compliant Crypto Custody”
Together, these developments signal a structural shift: stablecoins are no longer treated as experimental crypto assets. They are increasingly regulated as components of global financial infrastructure.
As a result, companies building stablecoin-based payment systems must integrate transaction monitoring, sanctions screening, and asset control capabilities from the infrastructure layer from the start.
External Risks Are Only Half the Picture
Regulatory pressure is only one side of the challenge.
Even if a business fully understands compliance requirements such as the Financial Action Task Force Travel Rule, sanctions screening, and transaction monitoring, operational risks still remain.
Unlike traditional banking systems, stablecoin payments run on open blockchain networks. Transactions are irreversible, wallet addresses are pseudonymous, and smart contracts introduce entirely new attack surfaces.
This creates a second category of risk that many companies underestimate: technical and operational vulnerabilities inside their own payment workflows.
In practice, businesses processing stablecoin payments often fall into a set of recurring security pitfalls from address poisoning attacks to token spoofing and approval exploits.
Understanding these vulnerabilities is essential before stablecoins can safely function as a reliable layer for B2B payments.
Operational Security Risks in Stablecoin B2B Payments: 5 Technical Traps Businesses Often Overlook
While regulatory reports often focus on systemic risks such as money laundering or sanctions evasion, companies that actually use stablecoins for B2B payments face another layer of exposure: technical attack vectors embedded in everyday wallet operations.
Unlike traditional banking systems where payments pass through multiple institutional checkpoints stablecoin transfers interact directly with blockchain infrastructure. This architecture enables fast and programmable payments, but it also means operational mistakes or small security gaps can lead to irreversible financial losses.
Several incidents over the past two years demonstrate how easily these vulnerabilities can be exploited.
1. Address Poisoning: When Copy-Paste Becomes a Million-Dollar Mistake
One of the most common operational attacks targeting crypto payments today is address poisoning, a tactic designed to exploit how users copy wallet addresses from transaction history.
Attackers generate wallet addresses that closely resemble a legitimate partner’s address often matching the first and last few characters. They then send a tiny amount of stablecoin (for example 0.0001 USDT) to the victim’s wallet so the malicious address appears in the recent transaction list.
Later, when the finance team needs to send another payment to the supplier, someone may simply copy the address from the previous transaction accidentally selecting the attacker’s address instead of the real one.
This mistake can redirect a large payment instantly.
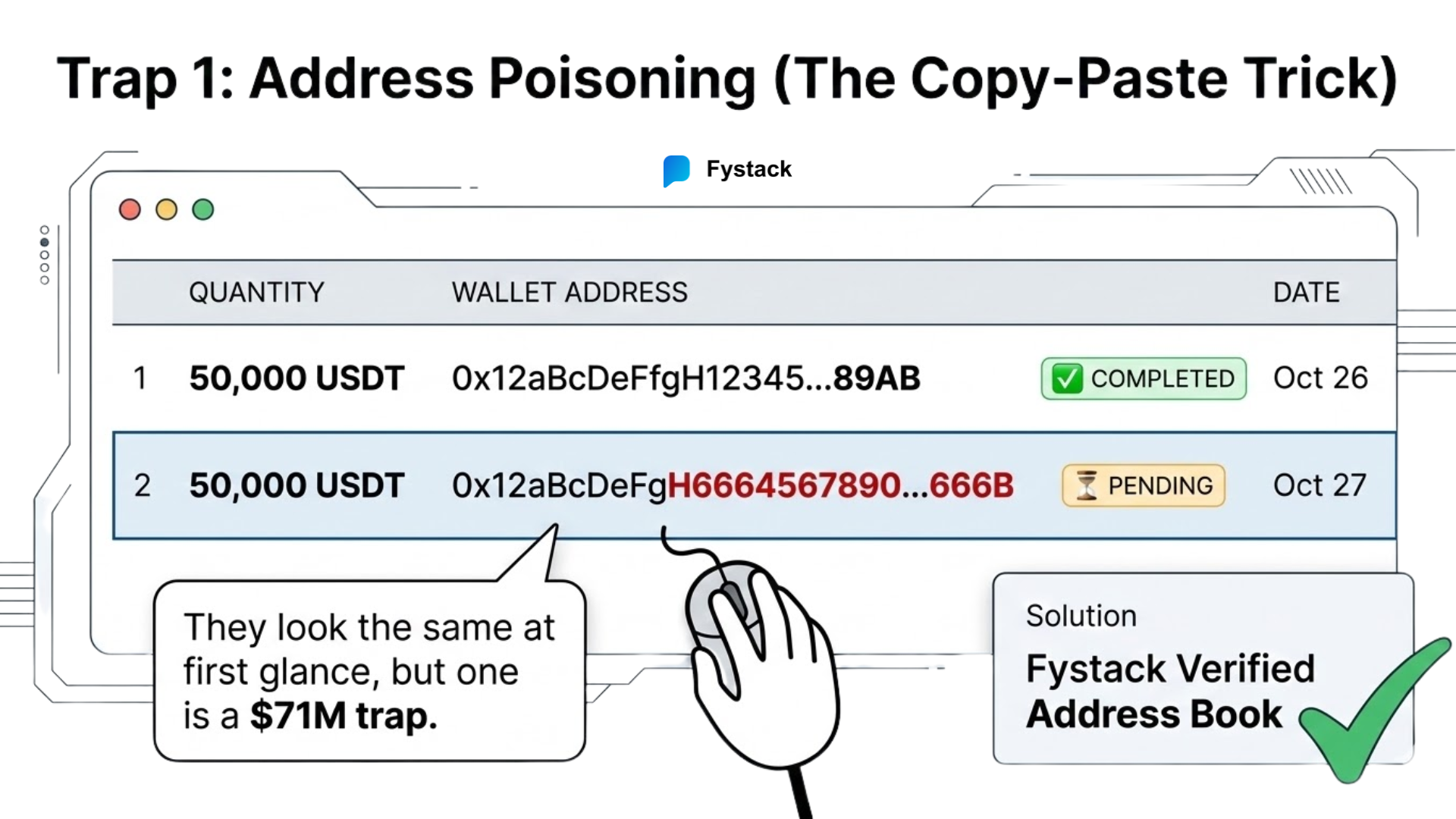
A striking example occurred in May 2024, when a trader attempting to transfer stablecoins copied a poisoned address from their transaction history and mistakenly sent $71 million in wrapped Bitcoin to the attacker’s wallet. The funds were briefly returned after negotiations, but the incident highlighted how simple UI behavior can create massive financial exposure.
For companies making recurring payments to suppliers, logistics partners, or service providers, the same mechanism can easily affect B2B stablecoin transfers.
Eliminate human error. Use Address Whitelisting and Verified Address Books within a managed treasury system. Never interact with the public transaction history for address retrieval; instead, use a "Deterministic Address" system where every counterparty is pre-verified and locked. Think of it as giving every customer a unique 'virtual sub-account' that automatically funnels into your main vault, keeping your books clean and your audit trail crystal clear.
2. Fake Stablecoin Tokens: When “USDT” Isn’t Actually USDT
Another trap emerges from how tokens are created on public blockchains.
On networks like Ethereum or Tron, anyone can deploy a token contract and assign it any name or symbol. This means malicious actors can create tokens labeled “USDT” or “USDC” that visually resemble legitimate stablecoins issued by Tether or Circle.
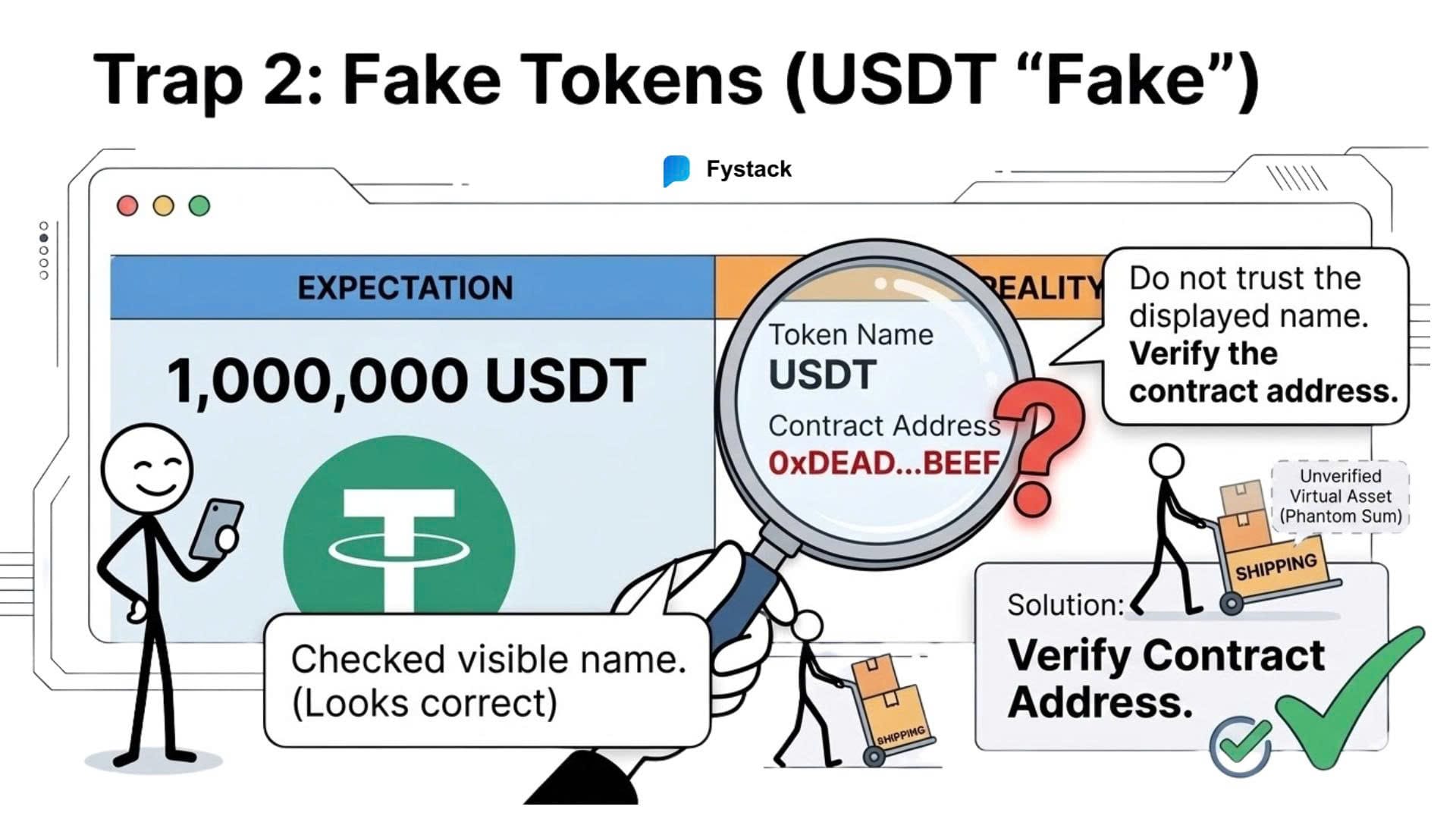
A company might open its wallet interface and see a balance showing something like “1,000,000 USDT”, leading the finance team to believe a supplier or customer has already settled a payment.
However, the token may actually originate from a completely unrelated contract with no liquidity and no redeemable value.
These fake tokens are frequently used in scams where attackers attempt to convince businesses that payment has already been made. If goods are shipped before verifying the token contract, the company effectively receives worthless assets instead of real payment.
Blockchain security researchers and wallet providers have repeatedly warned about these spoofed tokens, which have appeared across Ethereum, BNB Chain, and Tron ecosystems.
Secure payment infrastructure must include token contract verification. Wallet systems should automatically validate assets against official contract registries and ignore tokens that do not match the legitimate contract addresses published by stablecoin issuers.
3. Approval Exploits: The Invisible Permission That Drains Wallets
Another technical risk that many businesses underestimate lies in the approval mechanisms used by ERC-20 tokens, including most stablecoins.
Before a decentralized application or smart contract can move tokens from a wallet, the wallet must first sign an approval transaction that grants permission to spend those tokens. In many interfaces, this approval is presented as a routine step - something users click through quickly while interacting with payment tools or decentralized applications.
The problem is that many approvals grant unlimited spending rights, meaning the approved contract can later transfer any amount of tokens from the wallet without further confirmation.
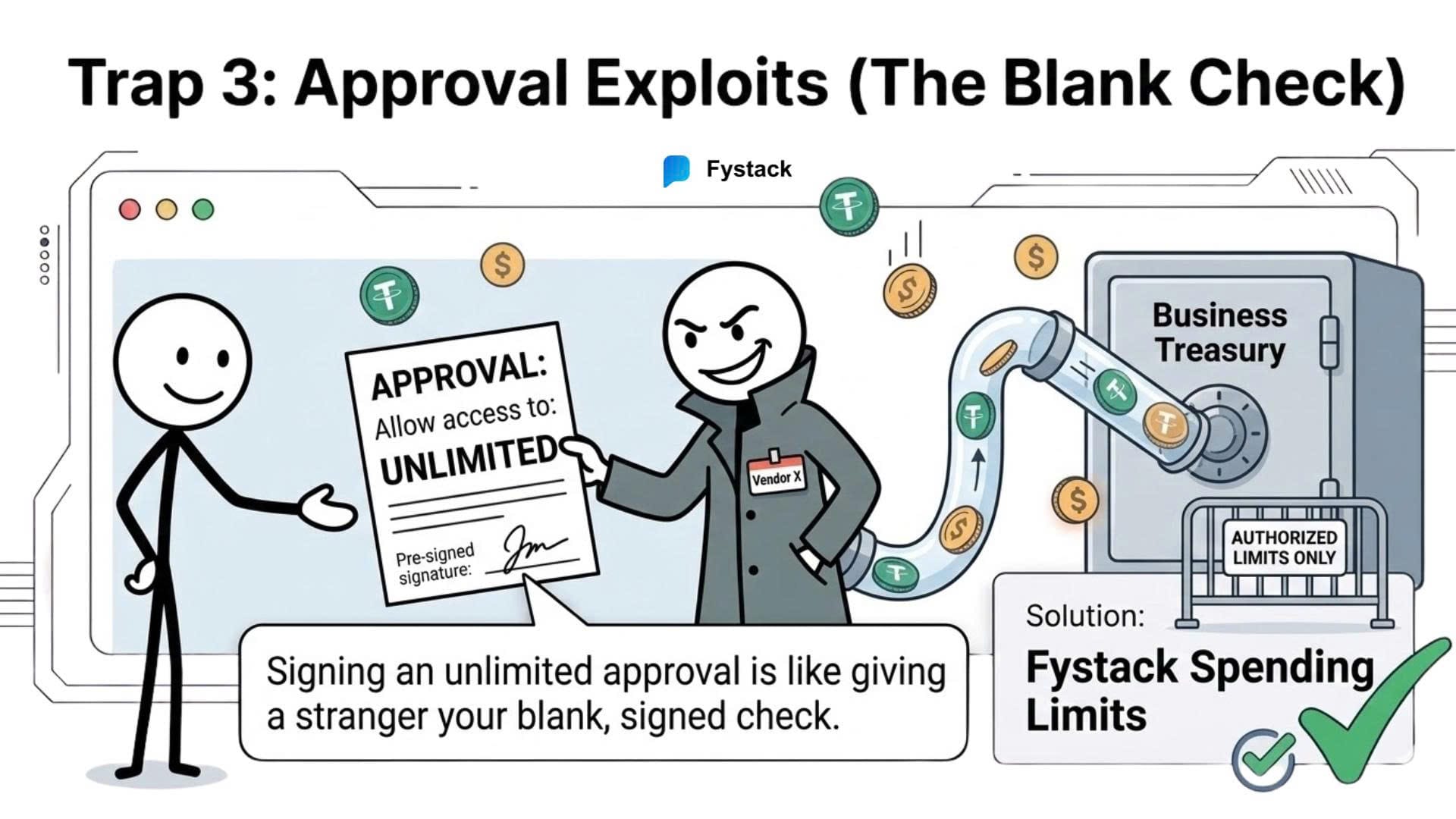
Attackers frequently exploit this mechanism by disguising malicious transactions as harmless actions such as:
- invoice verification
- payment confirmation
- vendor onboarding forms
- or “connect wallet to check transaction status”
Once the user signs the approval, the attacker gains permission to access the wallet’s stablecoins.
This attack pattern has already caused significant losses across the crypto ecosystem. In September 2023, the cryptocurrency exchange CoinEx suffered a major security breach that ultimately resulted in over $70 million in assets being drained after attackers obtained control of hot wallet permissions and moved funds through multiple token approvals and transfers. The incident illustrated how permission-based token systems can become a powerful attack surface when access control fails.
While the CoinEx breach involved compromised infrastructure rather than a phishing link, the underlying mechanism highlights the same architectural risk: once a contract has spending permission, it can move assets without additional wallet confirmations.
For companies using stablecoins for operational payments, this risk becomes particularly dangerous if treasury wallets interact with external smart contracts or payment interfaces.
Enterprise wallet systems should implement policy engines that control token approvals, including:
- approval limits instead of unlimited allowances
- multi-signature confirmation for approval transactions
- automated monitoring of outstanding token permissions
These controls ensure that even if a malicious contract receives approval, it cannot automatically drain the entire treasury.
4. Compliance Blindness: When Legitimate Payments Carry Illicit Funds
Technical exploits are not the only risk businesses face. In many cases, the danger lies in the origin of the funds themselves.
Stablecoins move freely across decentralized networks, meaning a payment received today may have previously passed through wallets linked to hacks, scams, ransomware operations, or sanctioned entities. If a company unknowingly receives these funds, the consequences can be serious.
Stablecoin issuers retain the ability to freeze tokens associated with illicit activity. When investigators identify funds connected to a hack or sanctioned entity, the issuer can blacklist the related wallet addresses, preventing the tokens from being transferred or redeemed.
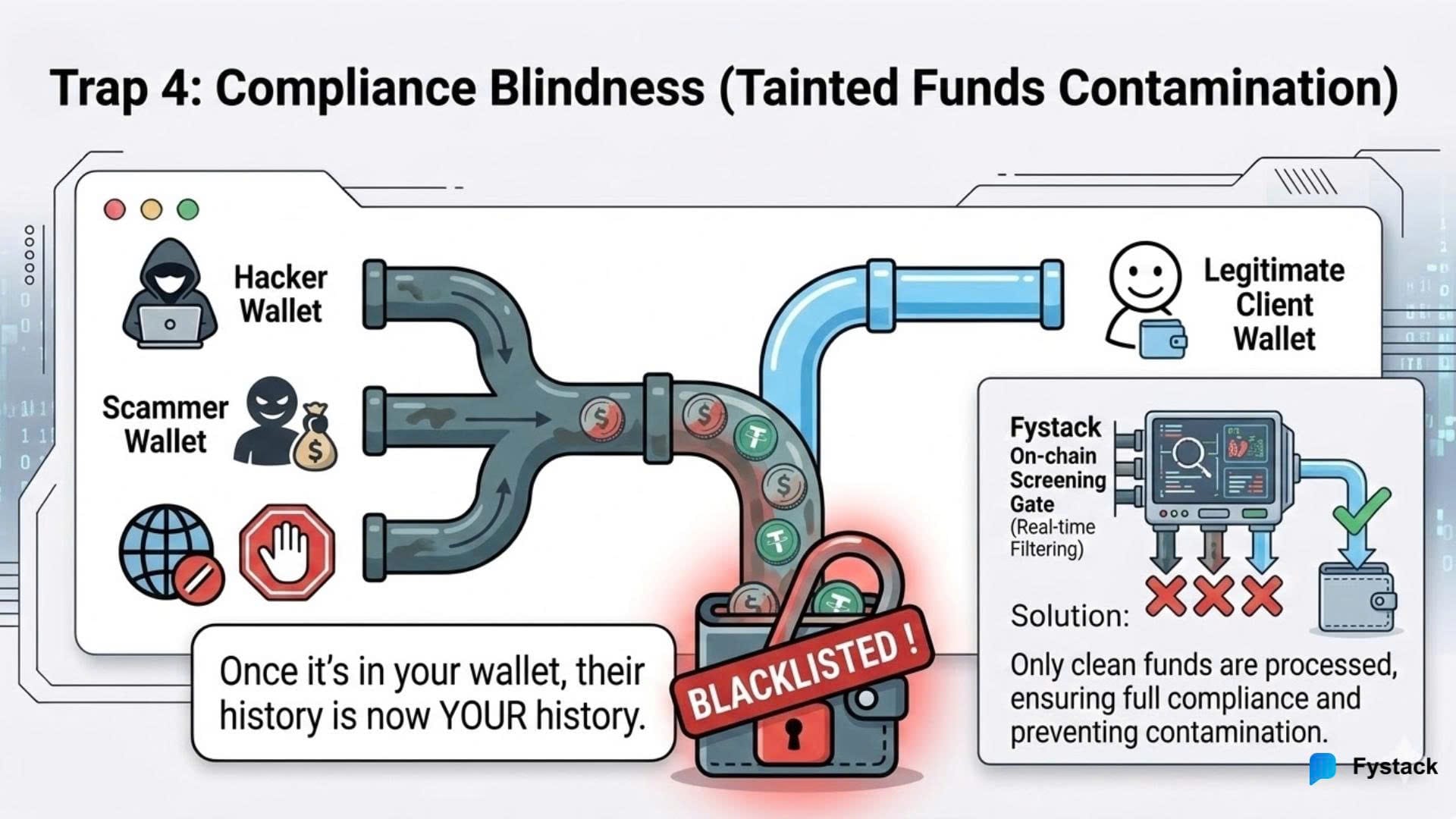
Several high-profile incidents illustrate this mechanism. After the 2022 Ronin bridge exploit, where attackers stole more than $540 million, portions of the stolen assets converted into USDC were frozen by issuers, preventing further laundering.
However, this mechanism can also affect innocent counterparties. Businesses may receive stablecoins through what appears to be a legitimate commercial transaction such as payments for inventory, logistics, or digital services without knowing the funds originated from criminal activity.
If those funds are later flagged, the tokens can become frozen or blacklisted, effectively turning legitimate revenue into unusable capital.
This reflects a broader shift in financial crime. Instead of remaining within isolated criminal networks, illicit funds increasingly blend into legitimate economic activity, particularly as businesses adopt new payment rails like stablecoins.
Companies processing stablecoin payments should integrate on-chain compliance screening before accepting funds. Transaction monitoring tools from firms such as Chainalysis or Elliptic can evaluate wallet histories and flag connections to high-risk sources in real time.
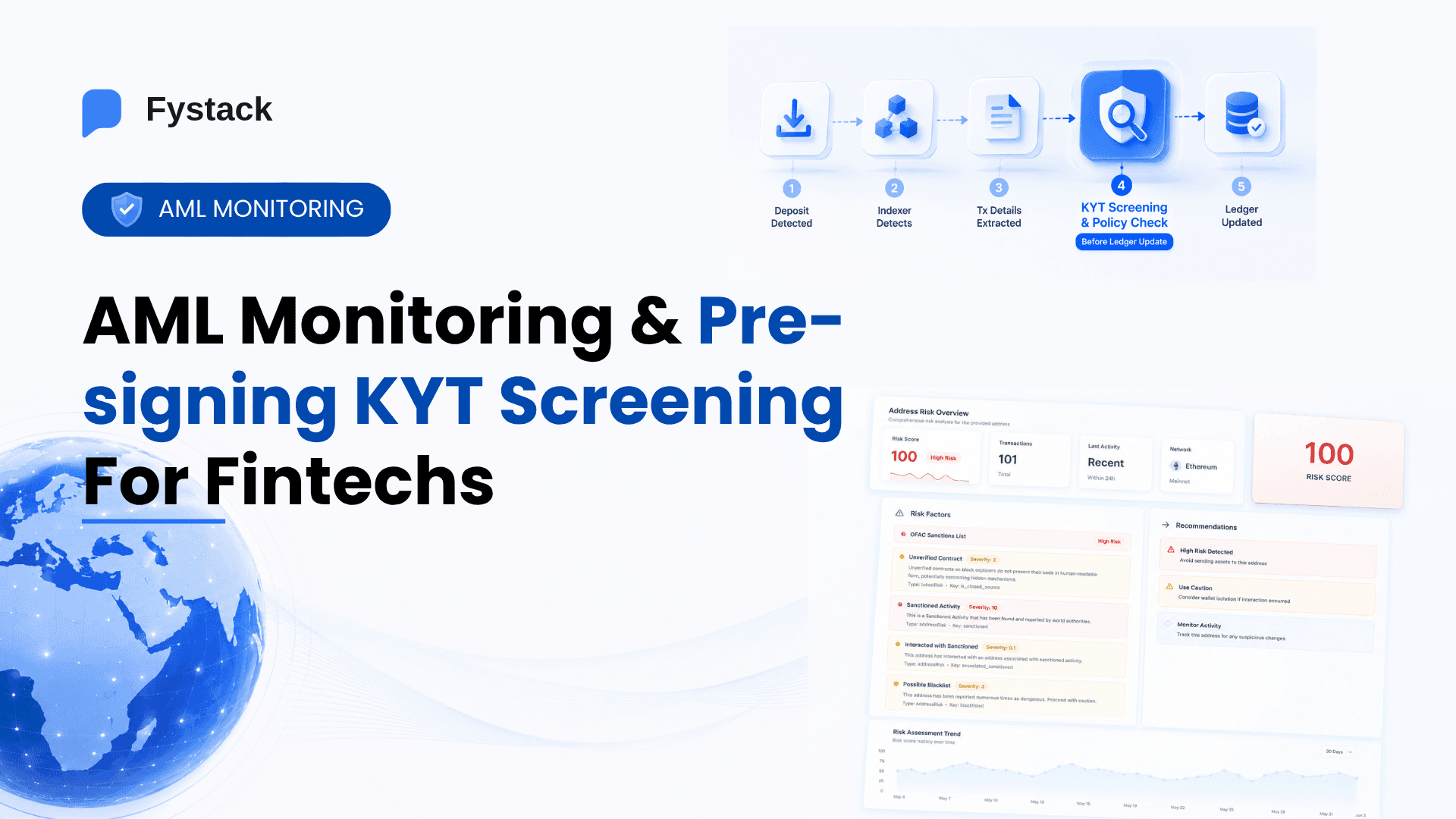
Fystack integrates similar KYT-based screening within treasury infrastructure, as described in “How MPC Wallets, KYT Screening, and Automated Consolidation Power Secure Crypto Payments”
This allows businesses to detect potentially tainted funds before they enter operational treasury wallets.
5. Dusting Attacks and Reputation Blackmail
The final trap is less about direct theft and more about compliance manipulation.
In a dusting attack, an attacker sends extremely small amounts of cryptocurrency - often fractions of a stablecoin - from wallets associated with suspicious or illicit activity to a target address.
Financially, these transactions are meaningless. But their presence in a wallet’s transaction history can trigger alerts from blockchain analytics systems that track connections between wallets.
Once a wallet becomes linked, however indirectly to suspicious addresses, it may be flagged with a risk score by compliance monitoring tools used by exchanges, custodians, and financial institutions.
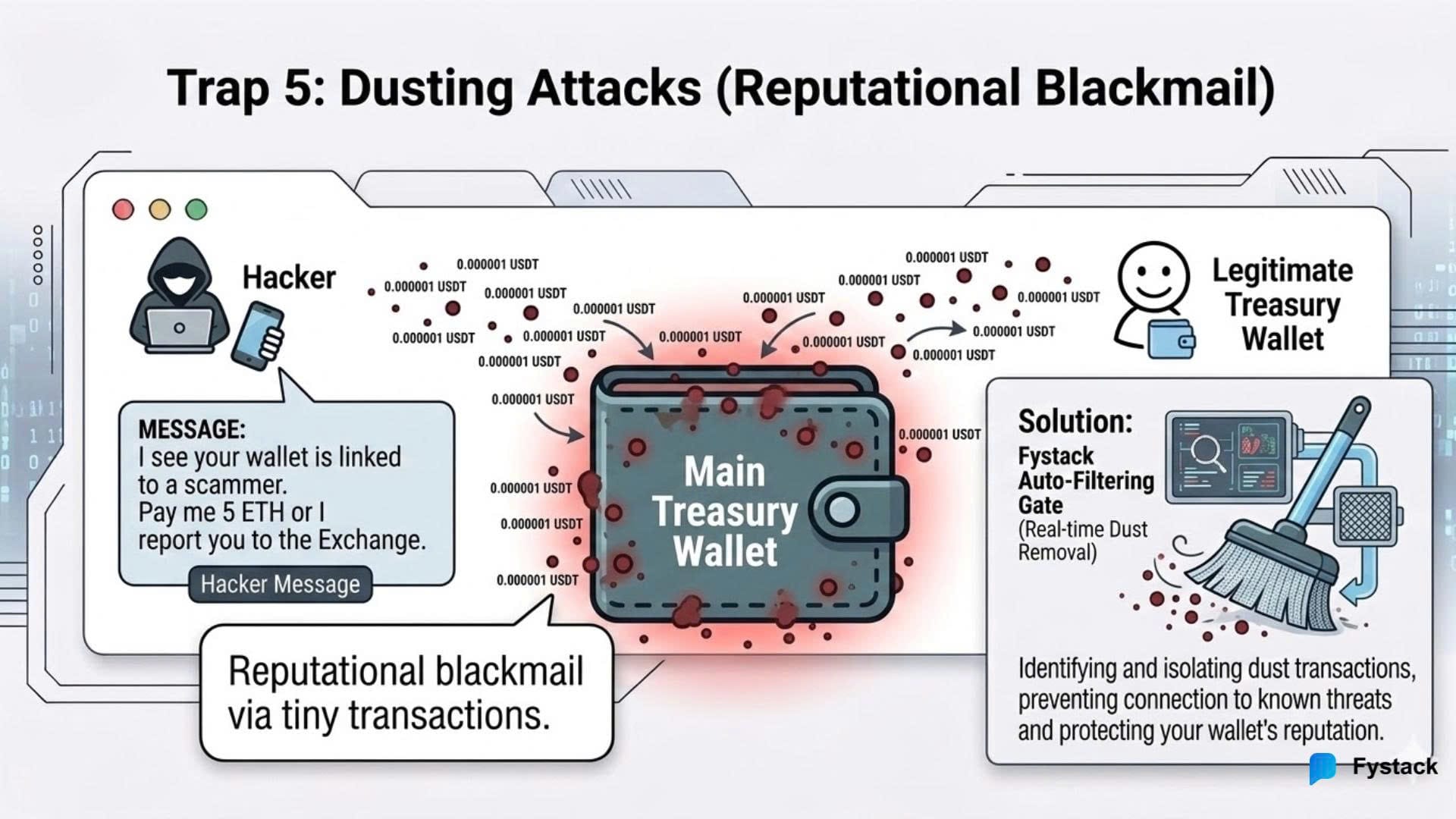
Attackers can exploit this by contacting the target company and threatening to report the wallet as suspicious unless a payment is made. In industries where access to regulated exchanges or banking partners is critical, even the appearance of AML risk can create reputational pressure.
While dusting attacks were initially used to deanonymize crypto users, they have increasingly evolved into a tactic for reputation-based extortion.
To reduce this risk, enterprise payment systems should implement advanced AML screening and transaction filtering capable of identifying suspicious micro-transactions. These systems allow businesses to quarantine or ignore dust-level transfers before they contaminate compliance analytics or internal transaction histories.
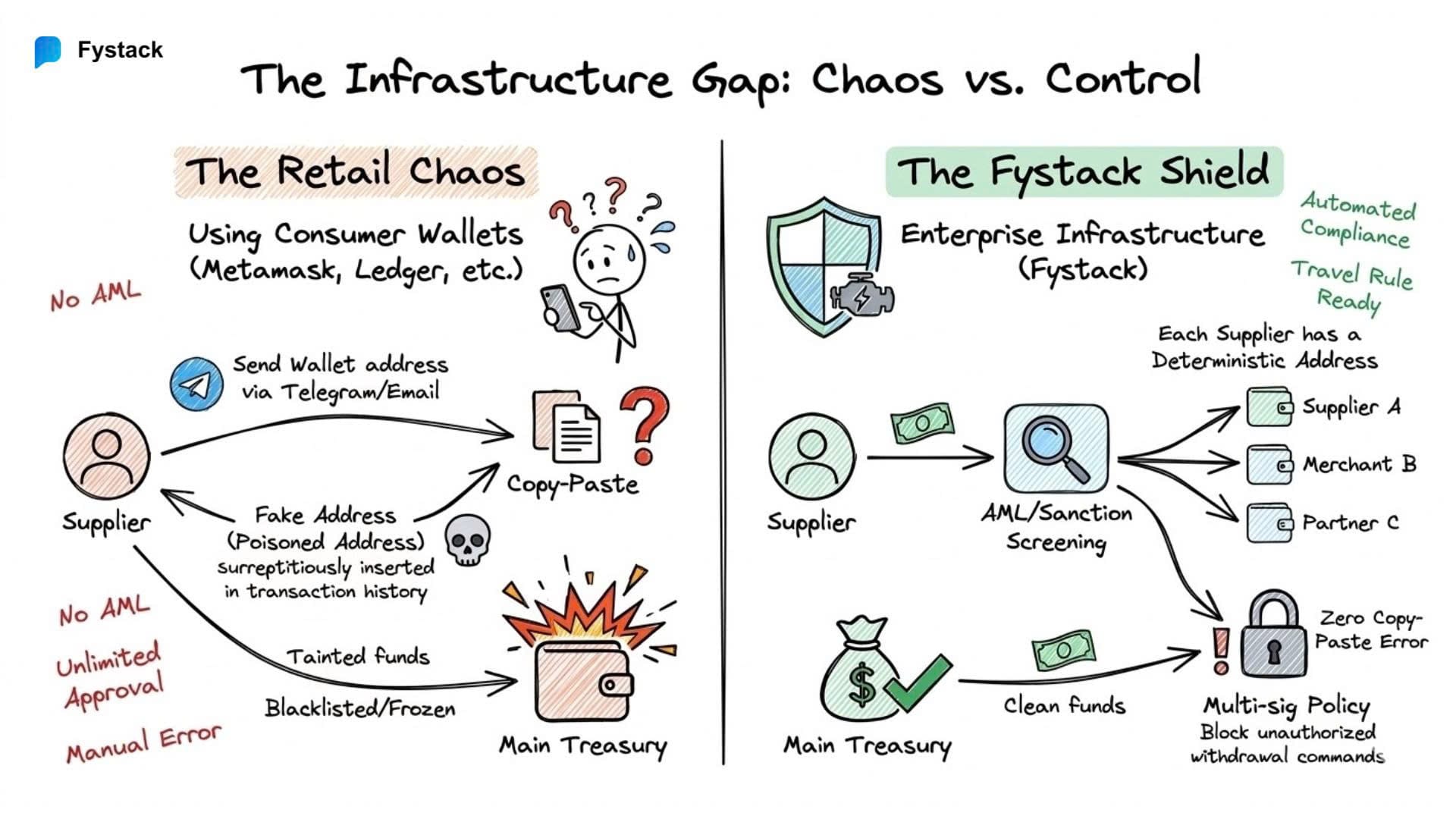
Infrastructure Gap: Why Consumer Crypto Tools Fail
Most crypto wallets were designed for individuals, not for companies managing treasury, compliance, and large-scale payments.
A retail user only needs to send and receive tokens. A business, however, must handle a very different operational reality: segregated funds, audit trails, policy controls, and regulatory monitoring.
When companies rely on consumer-grade wallets or exchange accounts for B2B payments, several problems quickly emerge:
- No automated transaction monitoring
- No Travel Rule support
- No policy-based approval controls
- No structured treasury segregation
- Limited auditability for finance teams
As stablecoins evolve into legitimate B2B payment rails, these limitations become operational risks rather than minor inconveniences.
What businesses need is not another wallet, but institutional infrastructure that integrates custody, treasury management, and compliance into a single system.
How Fystack Helps Companies Build Compliance-Ready Stablecoin Infrastructure
For many companies, the challenge is not understanding compliance requirements - it is implementing them within their payment infrastructure.
Monitoring tools, Travel Rule frameworks, and regulatory obligations such as those introduced under Markets in Crypto-Assets Regulation (MiCA) and the GENIUS Act stablecoin bill require systems that can manage transaction visibility, wallet control, and policy enforcement at scale.
This is where infrastructure design becomes critical.
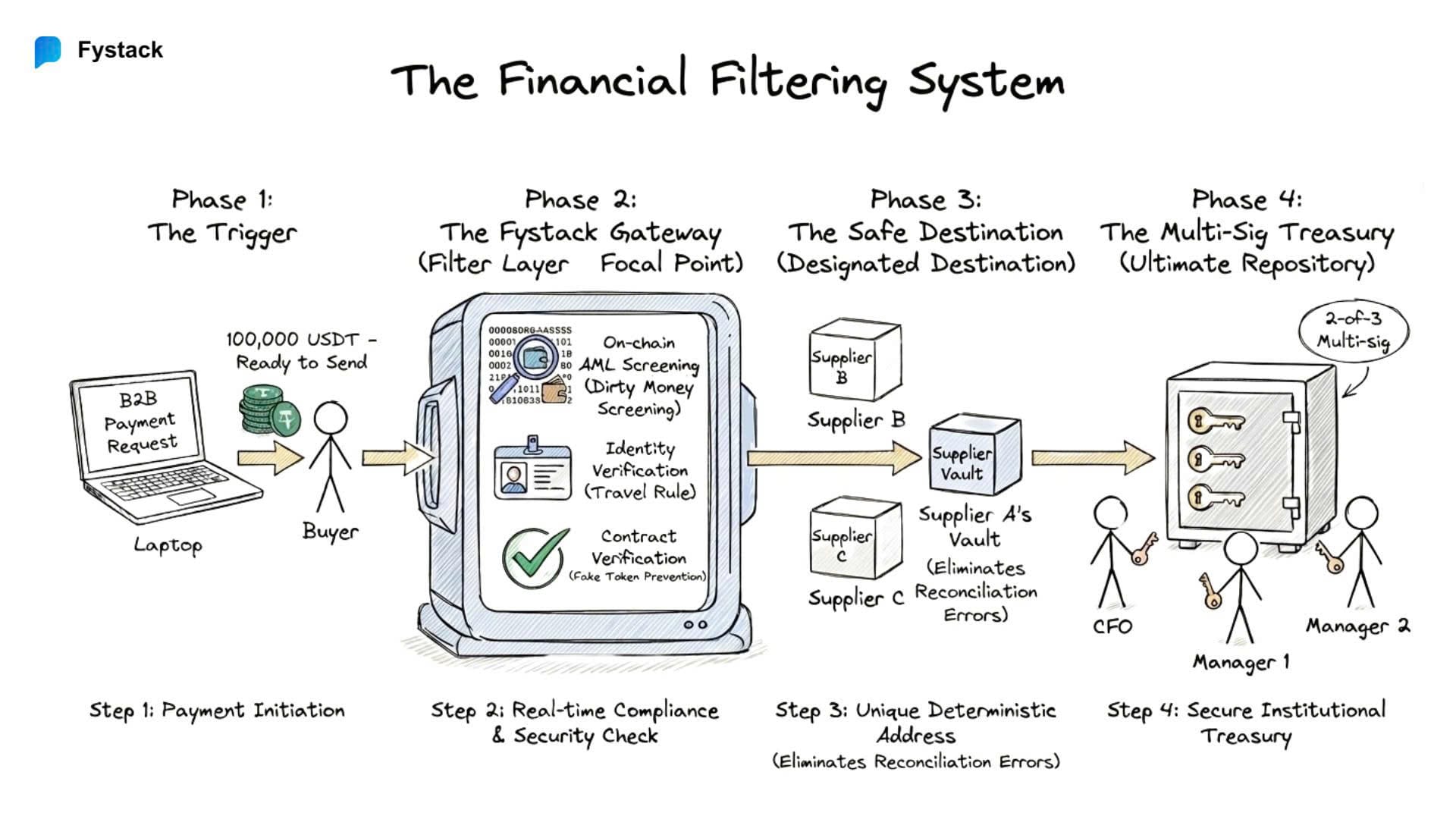
Fystack is built to help companies integrate stablecoin payments while maintaining operational and regulatory control from the start. Instead of treating compliance as a separate tool layer, Fystack embeds key capabilities directly into the wallet and transaction infrastructure.
This allows businesses to manage stablecoin operations with the same level of oversight expected in traditional financial systems.
Key capabilities include:
Deterministic Address Infrastructure
Fystack enables deterministic address generation, allowing businesses to assign unique blockchain addresses to users, merchants, or counterparties while maintaining centralized treasury control.
This structure improves transaction traceability and simplifies reconciliation — both essential for auditability and compliance monitoring.
Integrated Transaction Monitoring
Payment flows can be screened against risk signals and compliance policies before settlement, helping companies identify high-risk activity earlier in the transaction lifecycle.
Operational Control Over Funds
In cases involving fraud investigations, compliance alerts, or legal requests, infrastructure providers must be able to restrict or halt transactions when necessary. Fystack’s architecture enables businesses to maintain operational control over digital assets while supporting scalable payment flows.
Scalable Wallet Infrastructure
As payment volumes grow, companies may need to manage thousands or millions of deposit addresses across different blockchains. Fystack’s wallet infrastructure is designed to support this scale without sacrificing monitoring visibility or treasury control.
Stablecoins Are Transforming B2B Payments. But Infrastructure Must Evolve With Them
Stablecoins are quickly becoming a foundational layer for modern B2B payments. Their ability to move value globally within minutes, operate 24/7, and reduce settlement costs makes them increasingly attractive for cross-border trade, supplier payments, and digital commerce.
However, the same characteristics that make stablecoins efficient also introduce new operational and compliance risks. As highlighted in regulatory discussions and industry research from organizations such as Financial Action Task Force, blockchain-based payments can blur the line between legitimate commercial activity and illicit financial flows if proper safeguards are not in place.
For businesses, this means that adopting stablecoin payments is not simply a matter of integrating a wallet or accepting a new payment method. It requires building infrastructure that can:
- Monitor transactions for potential compliance risks
- Maintain traceability across payment flows
- Prevent operational threats such as address manipulation, token spoofing, or unauthorized approvals
- Align with emerging regulatory expectations such as the Markets in Crypto-Assets Regulation in Europe and evolving stablecoin frameworks proposed in the United States
Platforms such as Fystack helps businesses integrate stablecoin payments while embedding compliance, transaction monitoring, and scalable wallet management directly into their operations.
For companies exploring stablecoin-based B2B payments, the strategic question is no longer whether the technology will play a role in global commerce.
The real question is how to adopt it responsibly with infrastructure that is secure, compliant, and built to scale.
FAQ
Why are regulators increasingly concerned about stablecoins in B2B payments?
As stablecoins move from trading instruments into real-world payment infrastructure, regulators are concerned about how illicit funds could blend into legitimate commercial transactions. Reports from the Financial Action Task Force (FATF) highlight that cross-border stablecoin transfers, especially when combined with unhosted wallets, may create new risks related to money laundering, sanctions evasion, and fraud if proper monitoring and compliance frameworks are not in place.
Are stablecoins themselves illegal or unsafe for businesses to use?
No. Stablecoins are widely used for legitimate purposes such as cross-border payments, supplier settlements, and digital commerce. The concern raised by regulators is not the technology itself, but how stablecoins interact with open blockchain networks where both legitimate and illicit financial flows coexist. Without transaction monitoring and compliance safeguards, businesses may unknowingly interact with high-risk wallets or tainted funds.
How can companies unknowingly receive “dirty stablecoins”?
Because blockchain transactions are transparent but pseudonymous, a payment received from a legitimate counterparty may previously have passed through wallets linked to hacks, scams, ransomware, or sanctioned entities. If these connections are later discovered by investigators or blockchain analytics systems, stablecoin issuers may freeze the affected assets, potentially impacting innocent businesses that accepted the payment.
What is the Travel Rule and why does it matter for stablecoin payments?
The Travel Rule requires regulated crypto service providers to share identifying information about the sender and recipient when digital assets are transferred between institutions. For companies operating stablecoin payment infrastructure, compliance may require systems capable of transmitting transaction metadata, verifying wallet ownership, and supporting identity attribution across counterparties.
Can stablecoin issuers actually freeze funds?
Yes. Many fiat-backed stablecoins are issued by centralized entities that retain the ability to freeze or blacklist wallet addresses associated with illicit activity or sanctions violations. If funds linked to criminal investigations pass through a company's wallet, those assets may become frozen until the situation is resolved. This creates a new operational risk for businesses accepting stablecoin payments.
What technical security risks exist when companies use stablecoins for payments?
Beyond regulatory concerns, businesses also face operational risks inherent to blockchain-based payment systems. These include address poisoning attacks, fake token contracts impersonating legitimate stablecoins, unlimited token approval exploits, compliance exposure from tainted funds, and dusting attacks designed to manipulate AML monitoring systems. Without proper infrastructure safeguards, these risks can lead to financial loss or compliance issues.
Why are consumer crypto wallets not suitable for B2B payment operations?
Most retail crypto wallets are designed for individual users who only need to send or receive tokens. Businesses managing treasury operations require additional capabilities such as transaction monitoring, policy-based approvals, audit trails, Travel Rule support, and structured wallet segregation. Consumer-grade tools typically lack these features, creating operational and compliance risks when used for large-scale payments.
What infrastructure capabilities are required for compliant stablecoin payments?
Companies building stablecoin payment systems should implement infrastructure that includes transaction monitoring, sanctions screening, deterministic address management, policy-controlled approvals, and audit-friendly treasury segregation. These capabilities allow organizations to detect risky transactions early, maintain traceability, and align with evolving regulatory expectations around digital assets.
How can businesses protect themselves from operational mistakes like address poisoning?
Address poisoning attacks exploit how users copy wallet addresses from transaction histories. To mitigate this risk, companies should use deterministic address systems, verified address books, and address whitelisting within treasury infrastructure. These mechanisms ensure that payments are only sent to pre-approved counterparties rather than manually copied addresses.
What role does infrastructure play in making stablecoin payments safe for businesses?
As stablecoins become part of global financial infrastructure, companies need systems that combine blockchain efficiency with enterprise-grade controls. Infrastructure platforms such as Fystack help businesses integrate stablecoin payments while embedding compliance screening, transaction monitoring, deterministic address management, and scalable wallet orchestration into their operations.