Hyper Wallet vs MPC Wallet: Choosing the Right Wallet Model for Security and Scale
Phoebe Duong
Author

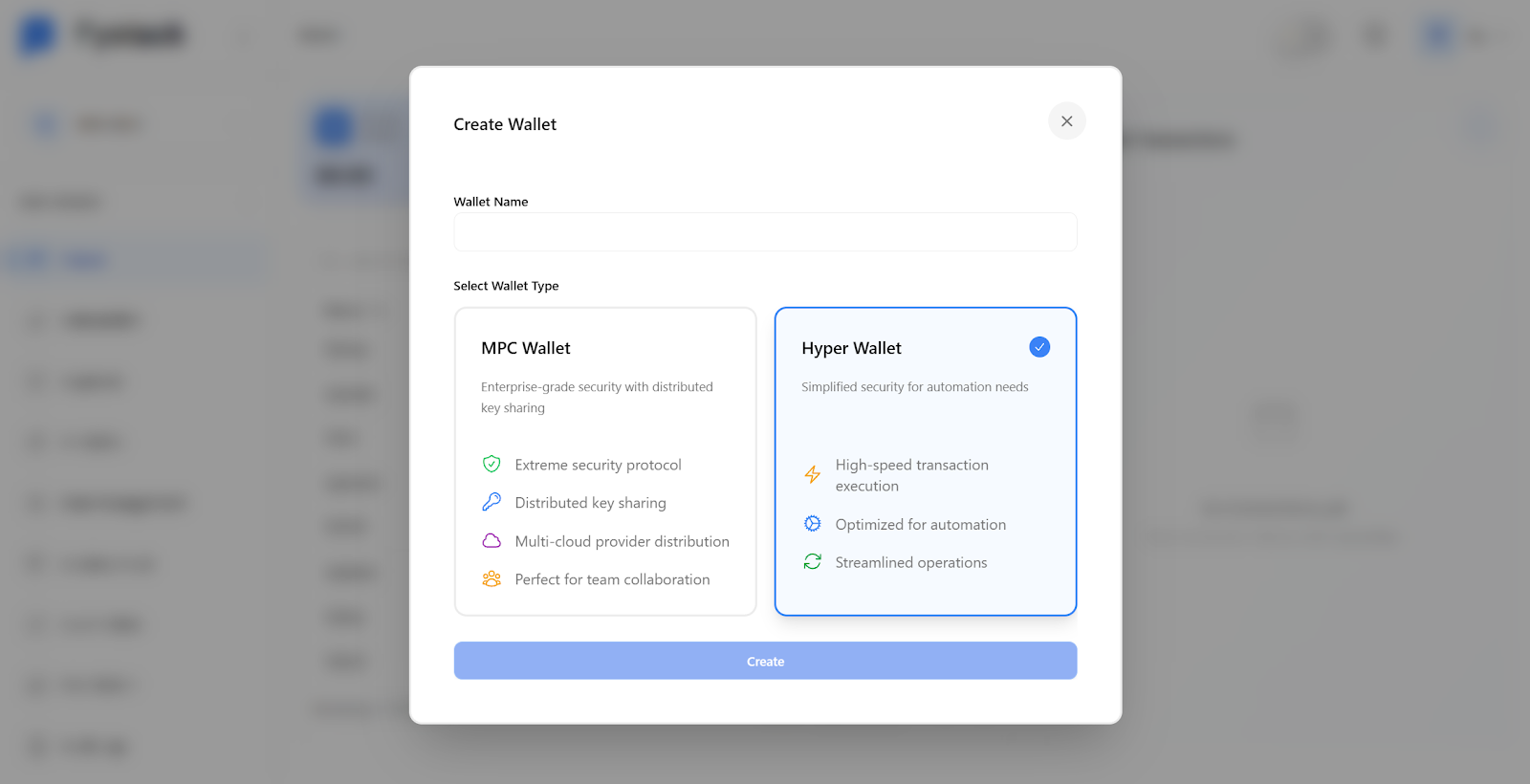
When creating a wallet on Fystack, teams are presented with two distinct options: MPC Wallet and Hyper Wallet. These are not interchangeable wallet types. Each is designed to solve a different operational problem in digital asset custody, especially when systems need to scale beyond a handful of wallets.
At a high level:
- MPC Wallet prioritizes security and institutional-grade asset protection
- Hyper Wallet prioritizes deposit efficiency and massive end-user scalability
Understanding when and how to use each wallet type is critical for building a secure, scalable on-chain system.
High-Level Overview: Two Wallet Types, Two Different Roles
Fystack provides a dual-wallet model to match real-world operational needs:
- MPC Wallet: Designed as the core custody layer for organizations. This is where treasury funds, operational balances, and high-value assets are secured.
- Hyper Wallet: Designed for large-scale user deposits. This wallet type enables teams to create thousands or millions of deposit addresses efficiently without the overhead of creating a full MPC wallet for every user.
Rather than forcing teams to choose between security and scalability, Fystack separates these concerns at the wallet architecture level.
MPC Wallet: Institutional-Grade Security for Core Funds
Role and Purpose
MPC Wallets are used as host wallets or main vaults within an organization.They are responsible for holding and protecting the organization’s core funds.
This wallet type is typically used for:
- Treasury management
- Exchange hot wallets
- Operational funds
- Custody of large balances
How MPC Wallet Security Works
MPC Wallets rely on Multi-Party Computation (MPC) to eliminate single points of failure.
- Private keys never exist in full form
- Key material is split into multiple cryptographic shares
- Shares are distributed across independent nodes
- Transactions require a predefined threshold of approvals (for example, 2-of-3)
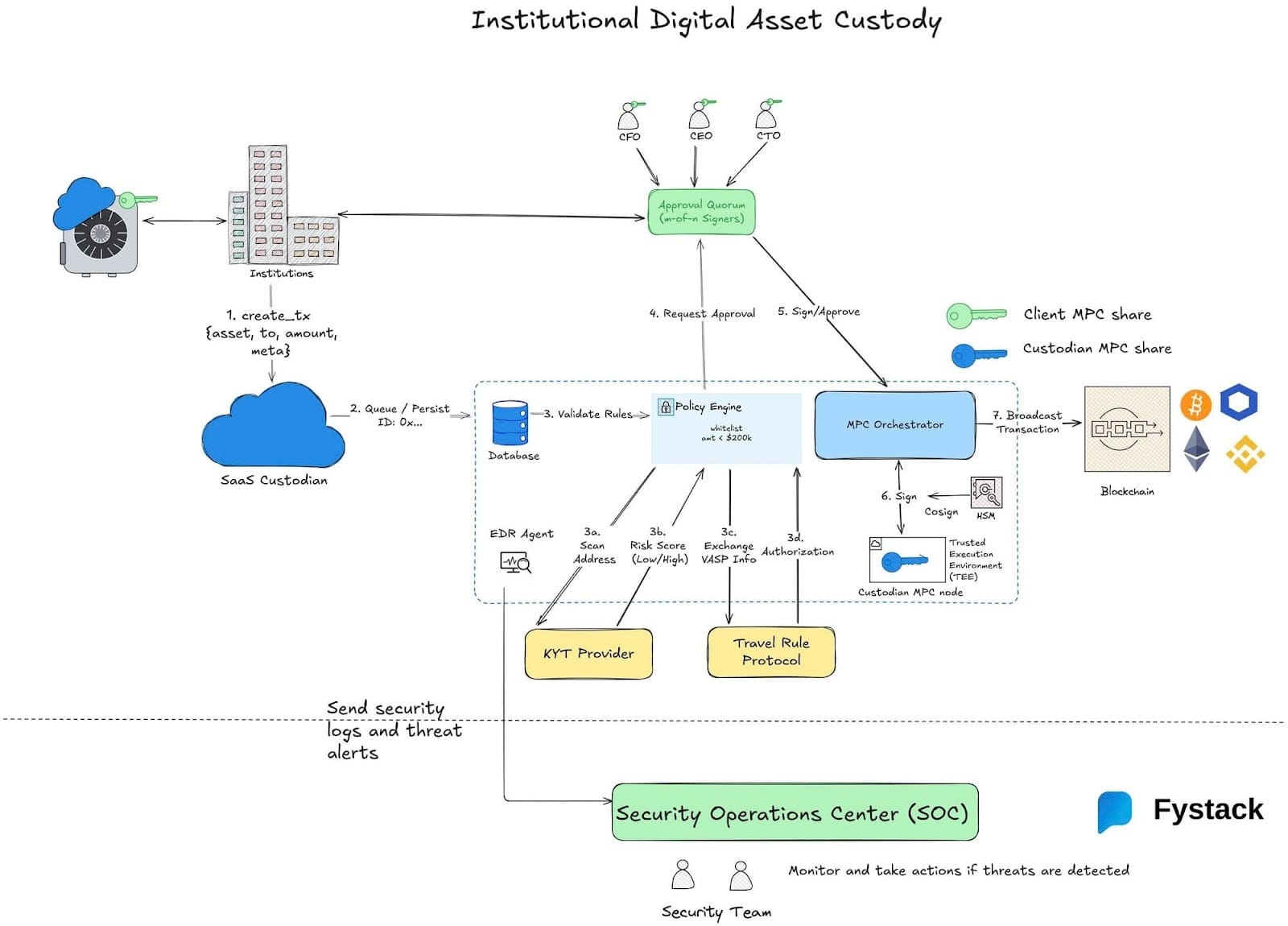
Even if one node is compromised, funds remain secure.
For teams evaluating MPC-based custody as part of a broader compliance and risk framework, this guide explains how institutional-grade MPC wallets support secure, auditable transaction workflows in production systems.
Target Users and Cost Positioning
Traditional MPC custody solutions in the market often target large enterprises with annual costs ranging from tens of thousands of dollars.
Fystack takes a different approach. It brings MPC-grade security to developers, startups, and small to mid-sized companies, allowing teams of 10 to 20 people to deploy secure custody infrastructure without heavy operational or financial overhead.
This architectural choice also reflects a broader shift away from SaaS custody models toward self-hosted infrastructure, especially for teams that want long-term control over keys, data, and compliance.
Hyper Wallet: Scalable Deposit Wallets for End Users
Role and Purpose
Hyper Wallets are designed to solve one specific problem: scaling user deposits.
In real-world applications, it is not feasible to create an MPC wallet for every end user.
For example:
- A crypto exchange with 1,000 users needs 1,000 deposit addresses
- A Web3 payment platform with 100,000 users needs 100,000 wallets
Hyper Wallets make this possible.
How Hyper Wallets Work
Hyper Wallets are deterministically derived wallets, optimized for instant creation and high-volume address management.
Key characteristics:
- Hyper Wallets are derived from a workspace-level seed phrase
- Each workspace has its own dedicated seed
- The workspace seed is protected by multiple layers of encryption
- Seeds are encrypted at rest using strong symmetric encryption
- Access to encryption keys is managed through secure key management systems
Wallet derivation follows standard paths (for example, BIP44 or SLIP-10 depending on chain)
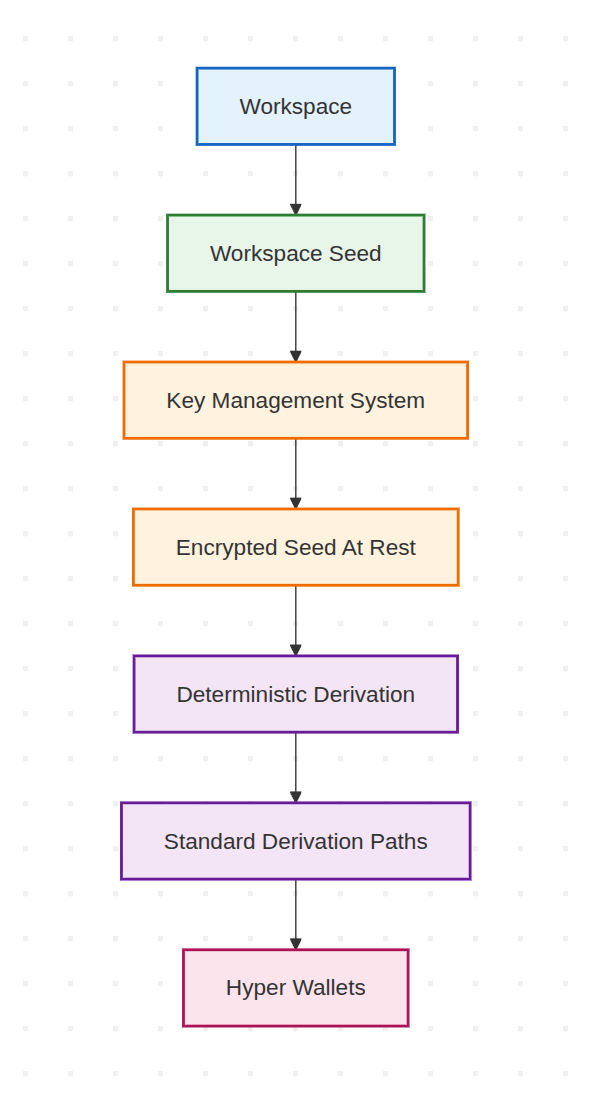
Because wallets are derived rather than generated through interactive protocols, they can be created instantly and programmatically, without running MPC key generation for each address.
This design enables teams to create thousands or millions of wallets while maintaining a consistent and auditable key hierarchy.
Security Model
Hyper Wallets are built with a clear security boundary:
- They are optimized for deposit and lightweight operations
- They are not intended to hold large balances long-term
- Funds are expected to be consolidated into MPC Wallets
By isolating user-facing deposit wallets from the core custody layer, teams reduce the attack surface while preserving operational scalability.
MPC Wallet Latency and Scalability: What Teams Need to Know
A frequent question when designing custody systems is:
“If MPC wallets are the most secure option, why not use MPC wallets for every user?”
The answer lies in latency and computational cost, not security weaknesses.
MPC Is Interactive by Design
MPC wallets rely on interactive threshold cryptography protocols. Unlike single-key wallets, MPC operations require multiple parties to coordinate cryptographically for both key generation and signing.
Each MPC wallet involves:
- Distributed Key Generation (DKG)
- Multiple cryptographic rounds
- Encrypted peer-to-peer communication
- Persistent state per wallet
- Coordination across independent nodes
This design is intentional. It maximizes security and fault tolerance, but it introduces measurable latency and infrastructure cost.
MPC Key Generation Latency (DKG)
Creating an MPC wallet is not a constant-time operation.
Typical production latency per MPC wallet:
MPC setup | Key generation latency |
2-of-2 (same region) | ~200–500 ms |
2-of-3 (same region) | ~500 ms – 1.5 s |
3-of-5 (same region) | ~1.5 – 3 s |
Cross-region nodes | ~2 – 6 s |
This latency is per wallet.
Creating:
- 1 wallet → fine
- 1,000 wallets → noticeable
- 100,000 wallets → operationally infeasible
Key generation also cannot be parallelized infinitely due to CPU, memory, and network constraints. Failures require retries, which further increase cost.
MPC Signing Latency (Per Transaction)
Each MPC signature requires interactive signing rounds.
Typical signing latency per transaction:
MPC setup | Signing latency |
2-of-2 (same region) | ~50–150 ms |
2-of-3 (same region) | ~150–400 ms |
3-of-5 (same region) | ~300–800 ms |
Cross-region nodes | ~500 ms – 2 s |
This is acceptable for:
- Treasury operations
- Hot wallets
- Operational transfers
But it becomes problematic when multiplied across thousands or millions of user wallets.
Why MPC Does Not Scale Per End User
Using MPC wallets per user introduces a multiplicative cost problem:
- Every wallet has permanent MPC state
- Every signing operation consumes coordinated CPU and network resources
- Concurrency increases non-linearly
- Infrastructure cost grows faster than user growth
In contrast, non-MPC wallets:
- Generate keys instantly
- Have near-zero signing latency
- Are stateless or lightweight
- Scale to millions of addresses
This is why no large exchange or payment system uses MPC wallets for individual deposit addresses.
How MPC Wallets and Hyper Wallets Work Together
Fystack is built around a hybrid custody model.
In practice, most teams use both wallet types together.
A common setup looks like this:
- Hyper Wallets are created for each end user to receive deposits
- MPC Wallets act as the secure central vault
- Funds are periodically consolidated from Hyper Wallets into the MPC Wallet
Automated Fund Management with Gas Station
To support large-scale operations, Fystack includes built-in automation mechanisms such as gas management and balance-based triggers, removing the need for manual fund handling.
In a typical workflow, Hyper Wallets are used as deposit endpoints for end users. When a Hyper Wallet receives funds, the system continuously monitors its balance against predefined thresholds configured by the team.
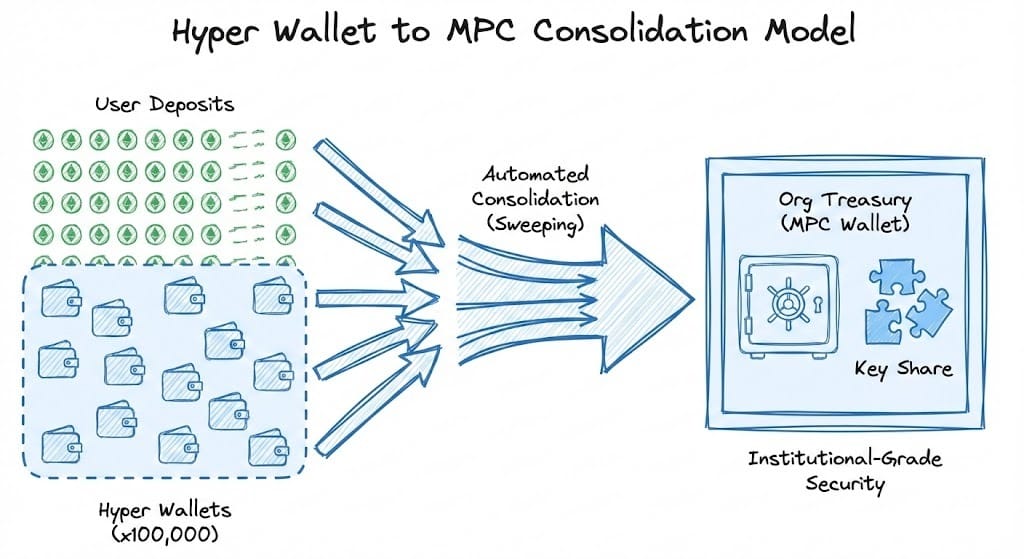
Once a wallet balance reaches the specified threshold:
- Gas fees are automatically provisioned through Fystack’s Gas Station
- No manual intervention is required to fund the wallet for transaction execution
- Assets are then programmatically consolidated into the designated MPC Wallet
This automated flow enables teams to:
- Maintain clean and predictable fund consolidation from user-facing wallets into the core custody layer
- Reduce operational risk caused by missed balances, delayed transfers, or manual errors
- Preserve centralized treasury control, while still supporting high-volume, decentralized deposit activity
By separating deposit scalability from treasury security, Fystack allows funds to move seamlessly from Hyper Wallets into MPC Wallets - ensuring that growth in user activity does not introduce additional custody or operational complexity.
Core Comparison: Hyper Wallet vs MPC Wallet
| Dimension | Hyper Wallet | MPC Wallet |
|---|---|---|
| Primary purpose | Scalable user deposit wallets | Core custody & treasury protection |
| Designed for | End-user deposits at massive scale | Organizational funds & high-value assets |
| Typical use cases | User deposit addresses, payment intake, on-chain accounts per user | Treasury, hot wallets, operational balances, vaults |
| Wallet creation model | Deterministic derivation from workspace seed | Interactive MPC key generation (DKG) |
| Creation speed | Instant (milliseconds) | Slow (hundreds of ms to seconds per wallet) |
| Scalability | Thousands to millions of wallets | Limited — not feasible per end user |
| Key architecture | Workspace-level seed, encrypted at rest | Key shares split across independent MPC nodes |
| Private key exposure | Exists in encrypted form via derivation | Private key never exists in full |
| Signing model | Single-party signing (derived key) | Threshold signing (e.g. 2-of-3, t-of-n) |
| Signing latency | Near-zero | 50 ms – 2s per transaction (depends on setup) |
| Security posture | Optimized for deposits, not long-term storage | Institutional-grade custody security |
| Balance expectation | Small, transient balances | Large, persistent balances |
| Failure tolerance | Standard key recovery via seed | Fault-tolerant against node compromise |
| Operational cost | Very low | Higher (compute, coordination, infra) |
| Compliance & auditability | Address-level traceability | Strong audit trails, approval workflows |
| Intended holding duration | Short-term | Long-term |
| Best practice | Consolidate funds into MPC Wallet | Act as final custody layer |
For teams building stablecoin or payment-focused platforms, choosing the right non-custodial custody architecture is critical. This overview compares leading non-custodial solutions and the operational trade-offs behind them.
Technical Details for Teams That Need Deeper Control
Hyper Wallet Technical Highlights
- Key derivation standards: BIP44 for EVM and Tron, SLIP-10 for Solana and Aptos
- Data encryption at rest using AES-256-GCM
- Each workspace uses a dedicated workspace seed
- Seeds are protected by a global encryption key managed through secure key management systems
MPC Wallet Technical Highlights
- Threshold signing model such as 2-of-3 or configurable t-of-n
- Secure node communication using encrypted messaging and key exchange
- Support for ECDSA and Ed25519 signatures
- Designed for multi-chain compatibility and high-assurance signing
Have questions about your custody setup?
Share what you are building via the form and explore how Fystack’s MPC wallets, KYT integrations, and consolidation engine fit your architecture.
Not ready yet?
Join our Telegram for product updates and architecture discussions:
https://t.me/+9AtC0z8sS79iZjFl
FAQ
What is the main difference between Hyper Wallet and MPC Wallet?
The main difference lies in purpose and scale. Hyper Wallets are designed for mass user deposits and high scalability, while MPC Wallets are built to secure and manage high-value organizational funds with institutional-grade security.
When should I use a Hyper Wallet instead of an MPC Wallet?
Hyper Wallets are ideal when you need to create thousands or millions of wallets for end users, such as deposit addresses for exchanges, payment platforms, or consumer-facing Web3 applications. They prioritize speed, scalability, and low operational overhead.
Why can’t every user wallet be an MPC Wallet?
MPC Wallets require multiple nodes to coordinate during key generation and transaction signing, which increases computational cost and operational complexity. Using MPC Wallets for every user would significantly raise costs without meaningful security benefits for small balances.
What is an MPC Wallet typically used for on Fystack?
MPC Wallets are commonly used as treasury wallets, hot wallets, or main vaults where assets are aggregated and managed centrally. They provide strong security guarantees and fine-grained approval controls for finance and operations teams.
How do Hyper Wallets and MPC Wallets work together?
Fystack uses a hybrid custody model. Hyper Wallets handle user-facing deposits at scale, while MPC Wallets act as the secure core vault. Funds can be automatically consolidated from Hyper Wallets into an MPC Wallet for centralized management and risk control.
Is Hyper Wallet secure enough for production use?
Yes. Hyper Wallets use industry-standard encryption (AES-256-GCM) for key storage and are suitable for handling end-user deposits. However, they are not intended for long-term storage of large institutional balances.
Can developers create Hyper Wallets programmatically?
Yes. Hyper Wallets are designed for developers and can be created programmatically via Fystack’s SDK, enabling automated wallet creation and management at scale.
Does Fystack support automation between Hyper Wallets and MPC Wallets?
Yes. Fystack supports automated workflows such as gas funding and balance-based consolidation, allowing funds to move from Hyper Wallets to MPC Wallets once predefined conditions are met.
Is this setup suitable for both startups and large organizations?
Absolutely. Startups can launch quickly without heavy infrastructure costs, while enterprises can scale securely with strong governance, auditability, and operational control using the same hybrid custody model.